Introduction
Calico is a third-party solution developed to provide flexibility and simplify configuring Kubernetes network connectivity. It is available on all the major cloud platforms and can be installed on bare metal servers.
Managing networks in Kubernetes is a complex job that requires experienced administrators. While plugins like kubenet offer some basic added functionalities, they do not provide features like network policy or cross-node networking.
This tutorial will show you how to install Calico on a Kubernetes cluster, focusing on the steps necessary to deploy it on a bare metal instance.
Prerequisites
- A system running a Linux server distribution (the article uses Ubuntu Server 20.04).
- Sudo privileges.
What is Calico?
Calico is an open-source CNI (Container Network Interface) plugin for network management developed by Tigera. The plugin aims to simplify Kubernetes networking while making it more scalable and secure.
The NetworkPolicy API, the out-of-the-box network policy management solution for Kubernetes, has a restricted set of features. Limited to a single environment, users can apply network policies created using this API only to labeled pods. Network rules deal only with protocols and ports and can be applied to pods, environments, and subnets.
Calico improves the default Kubernetes networking experience in the following ways:
- Rules can use actions like logging, restricting, or permitting. This feature provides administrators with greater flexibility in network configuration.
- Aside from ports and protocols, rules can specify port ranges, IPs, node selectors, etc., allowing for a more granular approach to networking.
- It extends the list of Kubernetes objects to which users can apply network policies with containers, interfaces, and virtual machines.
- It enables the use of DNAT settings and traffic flow management policies.
- Interoperability between Kubernetes and non-Kubernetes workloads is possible.
How to Install Calico on a Bare Metal Instance
All the popular cloud platforms, such as phoenixNAP's Bare Metal Cloud, OpenShift, Rancher, AWS, Azure, and the Google Cloud Platform, support Calico. Installing Calico on a cloud-hosted Kubernetes cluster is performed by downloading and applying the following file:
https://docs.projectcalico.org/manifests/calico-typha.yamlAside from cloud platforms, Calico supports bare metal installations. Follow the steps below to set up a Kubernetes cluster with Calico on a bare metal instance.
Note: The steps in this article were tested on a bare metal cloud server instance provisioned using the BMC portal. BMC is an IaaS solution that allows you to rent single-tenant, non-virtualized hardware resources immediately available for your projects.
Step 1: Install Kubernetes Management Tools
If you have a clean OS installation on your bare metal server instance, install dependencies and tools necessary for a Kubernetes cluster deployment.
1. Update the system repositories:
sudo apt update2. Install the apt-transport-https and ca-certificates packages, along with the curl CLI tool.
sudo apt install -y apt-transport-https ca-certificates curl3. Use curl to download Google Cloud GPG key and verify the integrity of downloads.
sudo curl -fsSLo /usr/share/keyrings/kubernetes-archive-keyring.gpg https://packages.cloud.google.com/apt/doc/apt-key.gpg4. Add the Kubernetes repository to your system.
echo "deb [signed-by=/usr/share/keyrings/kubernetes-archive-keyring.gpg] https://apt.kubernetes.io/ kubernetes-xenial main" | sudo tee /etc/apt/sources.list.d/kubernetes.list5. Refresh the package list.
sudo apt update6. Install the Kubernetes management tools - the kubelet node agent, the kubeadm command, and the kubectl CLI tool for cluster management.
sudo apt install -y kubelet kubeadm kubectl7. Use the apt-mark hold command to ensure the tools cannot be accidentally reinstalled, upgraded, or removed.
sudo apt-mark hold kubelet kubeadm kubectlStep 2: Install Docker
Kubernetes requires Docker for container management operations. Install Docker with the following command:
sudo apt install docker.io -yAdd your user to the docker user group when the installation is complete.
sudo usermod -aG docker [username]Note: For more detailed instructions for Docker installation, refer to How to Install Docker on Ubuntu.
Step 3: Disable Swap
For the kubelet node agent to function properly, the system swap must be disabled. Follow the steps below to disable swap on your system.
1. Open the /etc/fstab file in a text editor:
sudo nano /etc/fstab2. Look for the line starting with /swap.img and comment it out by typing # in front of it.
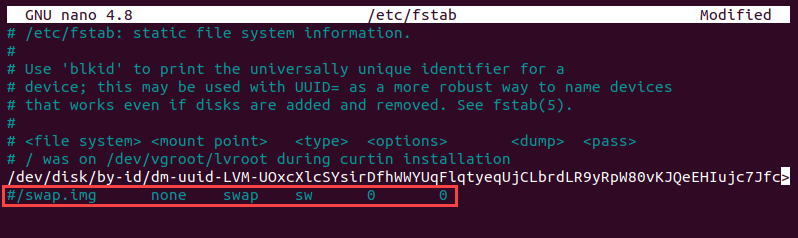
3. Save and exit the file. Editing /etc/fstab ensures the swap configuration persists after a system restart.
4. Disable swap for the current session by issuing the following command:
sudo swapoff -aStep 4: Initialize Kubernetes
1. Initialize the Kubernetes cluster using kubeadm init. Replace [server-ip] with the IP address of your server.
sudo kubeadm init --pod-network-cidr=[server-ip]/16
2. When the cluster initializes, create the .kube directory for your user.
mkdir -p $HOME/.kube
3. Link the contents of the admin.conf file to the user's home directory.
sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
4. Set the necessary permissions for the new file.
sudo chown $(id -u):$(id -g) $HOME/.kube/config
Kubernetes is now configured to work on your server instance.
Note: If you need a more comprehensive walkthrough for deploying a Kubernetes cluster, deploying a pod network, and adding worker nodes, read How to Install Kubernetes on Ubuntu and How to Install Kubernetes on Bare Metal Server.
Step 5: Install Calico Operator
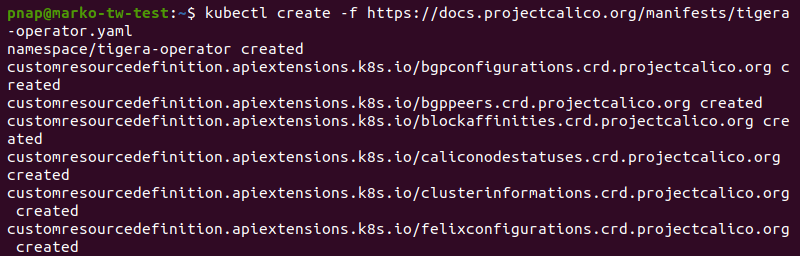
Install Calico using the kubectl create command and the tigera-operator.yaml available online.
kubectl create -f https://docs.projectcalico.org/manifests/tigera-operator.yamlThe installation creates multiple Kubernetes objects in the tigera-operator and calico-system namespaces.
Step 6: Apply Custom Resources
After deploying Calico, configure it to work with your network. Provide additional configuration by editing the custom-resources.yaml file.
1. Use the wget command to download custom-resources.yaml:
wget https://docs.projectcalico.org/manifests/custom-resources.yaml2. Open the downloaded file in a text editor.
nano custom-resources.yaml3. Edit the ipPools section in the file to reflect your configuration. Put the server's IP address in the cidr field.
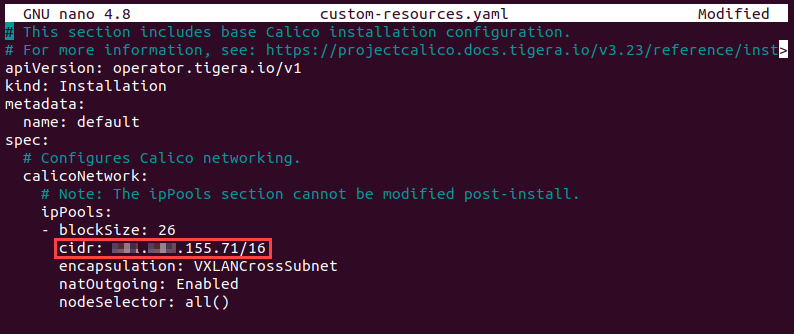
4. Save and exit the file.
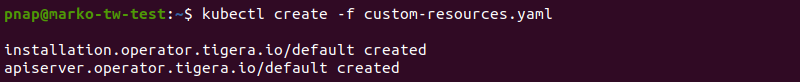
5. Apply the configuration with kubectl create.
kubectl create -f custom-resources.yamlThe output shows Kubernetes created two more objects.
Step 7: Confirm Successful Deployment
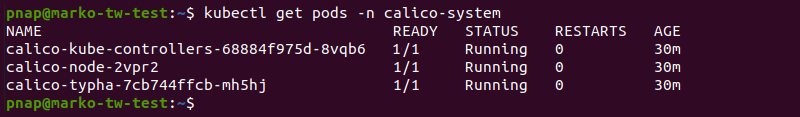
If successful, Calico deployment shows three running pods in the calico-system namespace. Check the status of the pods by typing:
kubectl get pods -n calico-systemThe output confirms the pods as ready and running.
Note: If the kube controllers pod stays in the pending state for too long, try issuing the following command:
kubectl taint nodes --all node-role.kubernetes.io/control-plane-
Removing the node-role.kubernetes.io/control-plane taint should resolve the problem.
Remove node taints from the node.
kubectl taint nodes --all node-role.kubernetes.io/master-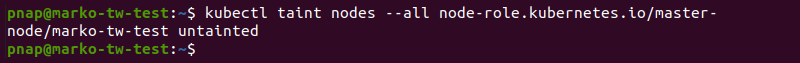
Use kubectl get to list the nodes and check their status.
kubectl get nodes -o wideThe output shows the node as ready.
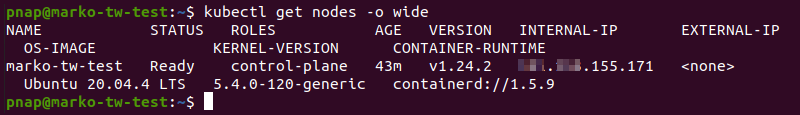
You successfully configured Calico to work with the cluster.
Conclusion
The article introduced you to Calico, a network management plugin offering a more flexible way to control Kubernetes network connectivity. The guide also provided steps to install Calico on a bare metal server instance running Ubuntu Server.
For more information about Kubernetes networking, refer to our Kubernetes Networking Guide.