Introduction
SFTP (Secure File Transfer Protocol) was introduced as a part of SSH version 2.0 to provide a secure way to transfer files between systems. It uses SSH to encrypt and protect the data it transfers.
In this tutorial, we will go over how SFTP works, how it compares to other file transfer protocols, and when you should use it.
How SFTP Works
When a client system requests a file transfer, SFTP creates a secure connection between the client and the SFTP server. This connection usually goes through port 22.
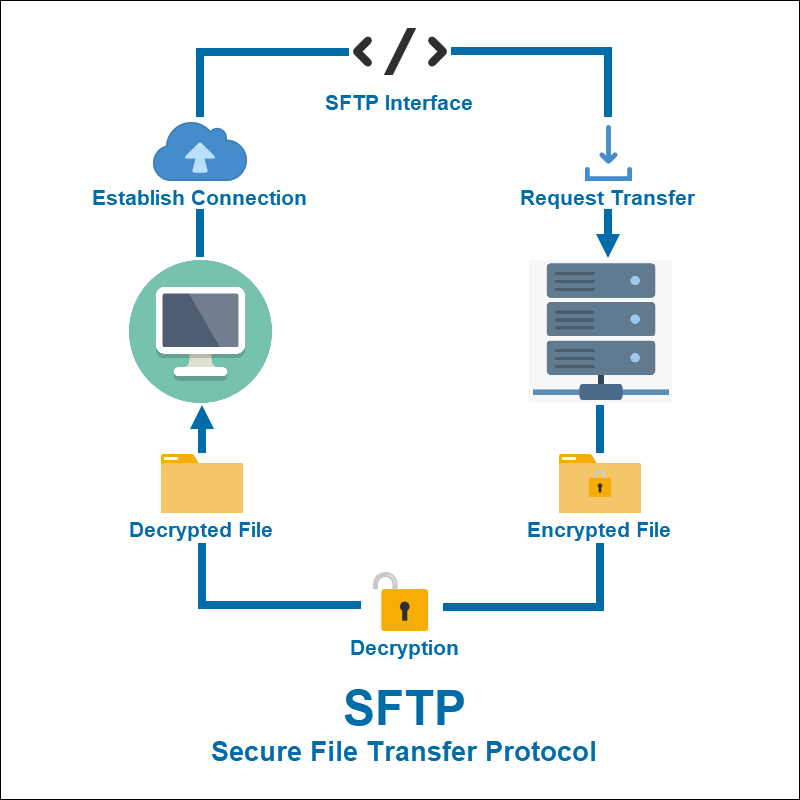
SFTP then uses the SSH protocol to encrypt the requested file and transfer it to the client. The client can decrypt and access the file using one of several authentication methods SSH offers.
These methods include a combination of user ID and password or a pair of SSH keys. Unlike FTP, the user ID and password are encrypted in SFTP.
Users can also set up the SFTP server in a way that does not require authentication, though this option is far less secure.
Note: Learn how to use public key authentication with SSH.
Transferring a file using SFTP consists of the following steps:
- Before transferring a file, the client and the server initiate a connection using an SSH authentication method.
- Once the connection starts, the client tests the SSH access to the server.
- If the test is successful, the client and the server establish an SFTP connection.
- The SFTP client switches over to the SFTP interface.
- The client opens an SFTP session using port 22.
- The client initiates the file transfer.
How Does SFTP Compare to FTP?
SFTP offers a more secure alternative to FTP when it comes to transferring files over the Internet. It is important to note that SFTP is not a different version of FTP but rather a completely different protocol.
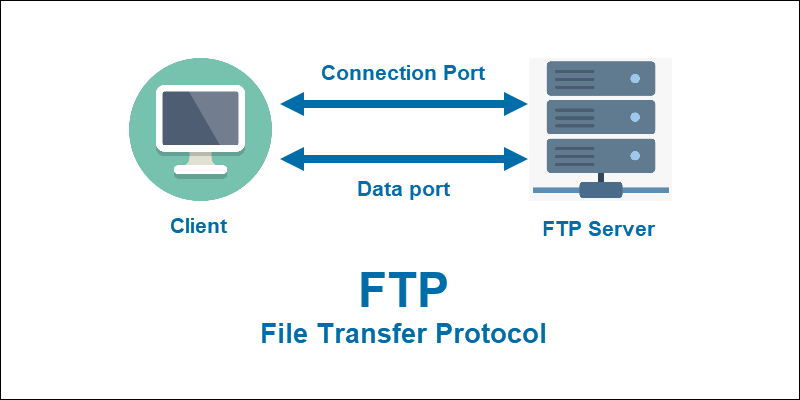
Unlike FTP, which does not use any form of encryption, SFTP uses SSH to encrypt the data it sends. This protects data and ensures it complies with safety regulations, such as PCI-DSS, HIPAA, GDPR and CCPA.
When establishing a connection, FTP uses two ports. One serves to establish and maintain a connection to the client, while the other transmits the data from the FTP server.
On the other hand, SFTP only uses one port to connect and send data. This method minimizes the risk of data being intercepted during transfer by reducing the number of potential targets.
Note: Check out our posts How to Use SFTP Commands and Options and How to Use the Linux ftp Command to learn everything about using SFTP and FTP.
Why Use SFTP?
The most obvious reason to use SFTP is that it provides more security than other file transfer protocols. This is especially important for clients that need to comply with security regulations when transferring files.
SFTP offers more advanced features, such as pausing and resuming file transfer. It also allows users to perform basic administrative tasks on remote systems, like creating, viewing, and managing files and directories and changing file permissions. Additionally, SFTP increases speed and efficiency since it supports transferring large and bulk files faster than other similar protocols, such as FTP.
In its earlier versions, SFTP had problems with speed and scalability compared to protocols such as SCP. This was because every file transfer needed to be separately authenticated. However, newer solutions like cloud SFTP help improve scalability.
Finally, SFTP helps users access file meta-data, like size, date and time, or permissions. Other transfer protocols have workarounds to enable meta-data, but with SFTP, this option is fully supported.
Conclusion
While FTP, SCP and similar protocols offer a reliable way to transfer data over the Internet, SFTP improves on this by adding a layer of encryption and increasing security. If you are looking for a secure way to transfer files, SFTP is the way to go.