Introduction
Ansible is an Infrastructure as Code tool that allows you to monitor and control a large number of servers from one central location.
The key advantage of Ansible over other similar systems is that it uses SSH and YAML configuration files, and doesn’t require any additional specialized software.
This tutorial explains how to install and configure Ansible on Ubuntu 20.04.
Prerequisites
- A system running Ubuntu 20.04
- Access to the command line / terminal window
Step 1: Configure Ansible Control Node, Host, and SSH Key Pair
Before you install Ansible on Ubuntu, make sure you have a couple of things set up. The configuration requires an Ansible control node and one or more Ansible hosts.
Note: The Ansible control node gives you control over Ansible hosts. It can be a dedicated server or a local machine with Ubuntu 20.04 installed.
Configuring the Ansible Control Node
To set up the Ansible control node, log in as root user. Create another (non-root) user with administrative privileges, and then add an SSH key pair for the new user.
1. As root, add an administrator-level user for the control node. Use the adduser command:
# adduser [username]2. Define a strong account password and, optionally, answer a list of questions.
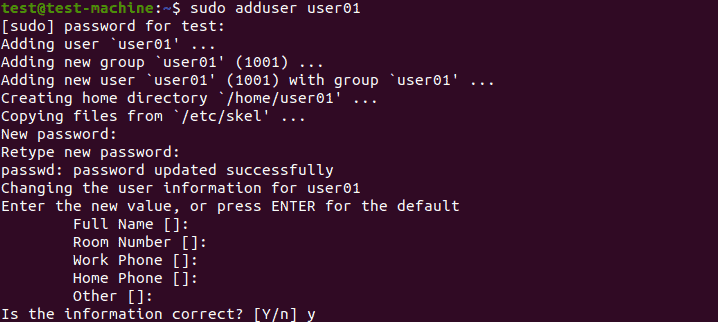
3. Press Enter to skip any of the fields you don’t want to fill out at the moment.
4. The new account is ready. Now, assign administrative access to the account. The following command assigns superuser privileges, allowing the account to use the sudo command:
# usermod -aG sudo [username]With the sudo command, the new user is now able to perform administrative tasks. Log into the new user account when you want to use the Ansible control node.
Setting up an SSH Key pair
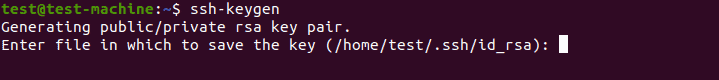
1. Enter the following command in the Ansible control node terminal:
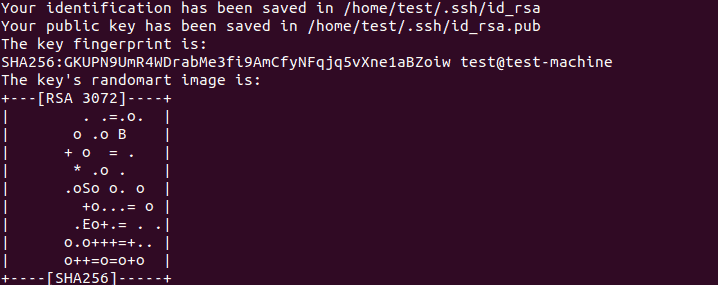
$ ssh-keygen2. Hitting Enter shows the following output:
3. The system displays the output below if you already have an SSH key pair set up. Decide whether to overwrite the existing SSH key pair.

Note: Overwriting makes the previous SSH key pair unusable. Since this is an irreversible process, make sure you have no further need for the old keys before you confirm.
4. Finally, you are prompted to provide a passphrase. We highly recommend adding a strong passphrase to avoid any security issues in the future:
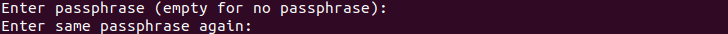
The output should be similar to the one below:
Configuring an Ansible Host
Ansible hosts are remote servers that are monitored and controlled by the Ansible control node. Each host needs to have the control node’s SSH key in the system user’s authorized keys directory.
1. The easiest method of setting up an SSH public key is to copy it using the ssh-copy-id command:
$ ssh-copy-id username@remote_host2. The first time you use this command, you may see the following message:
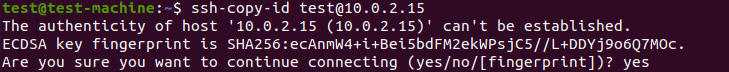
This kind of output is normal, and it appears when you connect to a new remote host for the first time.
3. To continue, simply enter yes and hit Enter.
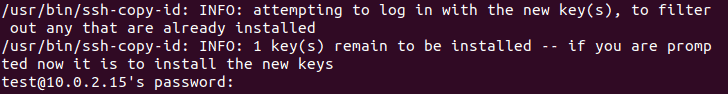
The utility now searches for the public part of the key pair generated during the previous step.
4. Once it finds it, enter the remote host account’s password.
5. Confirm the password by hitting Enter. The utility uploads the public key to the remote host’s account, and shows the following output:
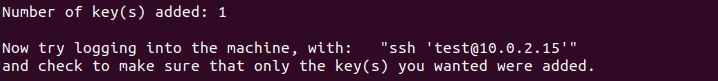
Note: For security purposes, the password won’t be displayed as you type it.
Step 2: Install Ansible
1. Make sure your system’s package index is up to date. Refresh the package index with the command:
$ sudo apt update2. Next, install Ansible on Ubuntu with the command:
$ sudo apt install ansible3. The installation will prompt you to press Y to confirm, with the rest of the installation process being automated.
Once installed, the Ansible control node can manage the remote hosts.
Step 3: Setting up the Inventory File
Set up an inventory file of remote hosts to enable Ansible to communicate with them.
Note: The inventory file contains all the information about the remote hosts you manage through the Ansible control node. You can store up to several hundred hosts, organize them into groups and subgroups, and set variables specific to the groups you had set up. For an in-depth overview of creating files on remote hosts, please refer to our article How To Create A File In Ansible.
1. To access the inventory file, use the following command in the control node’s terminal:
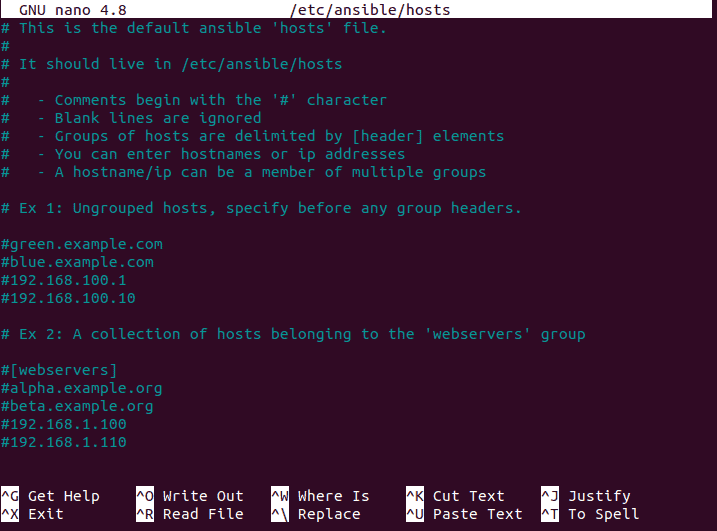
$ sudo nano /etc/ansible/hostsThe default path for the Ansible inventory file is /etc/ansible/hosts, but you can also provide a custom path by using the -i parameter:
2. With the inventory file open, you can now start adding remote hosts that your control node will manage. The default Ansible inventory file starts by listing general advice and examples on building a list of remote hosts:
3. Scroll to the bottom of the file to add new hosts and sort them into categories. When adding hosts and categories, use the following format:
[category name]
server_name ansible_host=[server_ip]In this example, we added a remote host called server1 by using its IP address, and sorted it into the [servers] category:
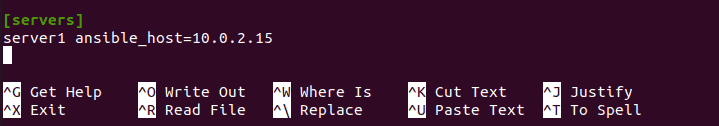
4. Once you are done adding items to Ansible’s inventory, hit Ctrl+X and then press Y to save the inventory file.
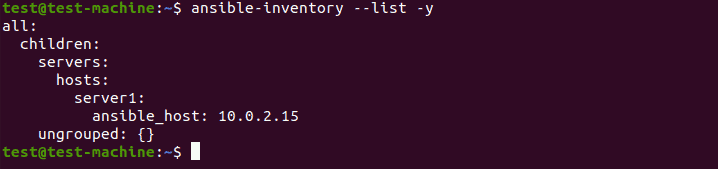
5. After you’ve set up the inventory file, you can always check it again by using:
$ ansible-inventory --list -yThe terminal window will display an output listing the hosts infrastructure:
Step 4: Testing the Connection
The final step is making sure the Ansible control node connects to the remote hosts and run commands.
1. To test the connection with the hosts, use the following command in the terminal on your control node:
$ ansible all -m ping2. Under normal circumstances, this will be the non-root user we already set up in Step 1. If for any reason you need to test the connection as the default root user, you can include the -u argument with the command:
$ ansible all -m ping -u rootRunning the command produces an output similar to the following:
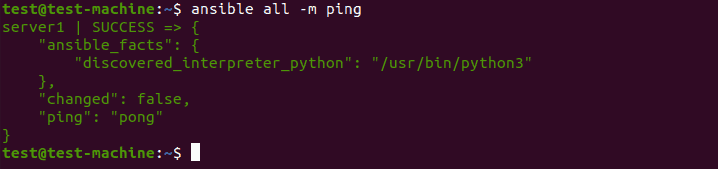
3. If you’re connecting to the remote hosts for the first time, Ansible will ask you to confirm that the hosts are authentic. Once prompted, type ‘yes’ and hit Enter to confirm the authenticity.
When all the remote hosts reply with a ‘pong’ back, you are ready to start running commands through the Ansible control node.
Conclusion
After following the steps in this guide, you’ve successfully installed Ansible on Ubuntu 20.04.
You are now ready to use Ansible to execute commands and playbooks on remote servers.